Igiko provides basic functionality for managing hosts and virtual machines (VMs). For a user, these are mainly features for status management (start, shut down, restart, etc., a host/VM), as well as features for software installation and deletion management. For an administrator, they also involve management of user permissions to access various objects. This article gives an overview of all available features and specifics of their use.
From the previous article, you could find out how to add hosts to your app. The administrator can also delete hosts and edit the credentials of the user under whose name a remote connection to the host is established. This is necessary if the user password has been changed or if you want to change the user altogether.
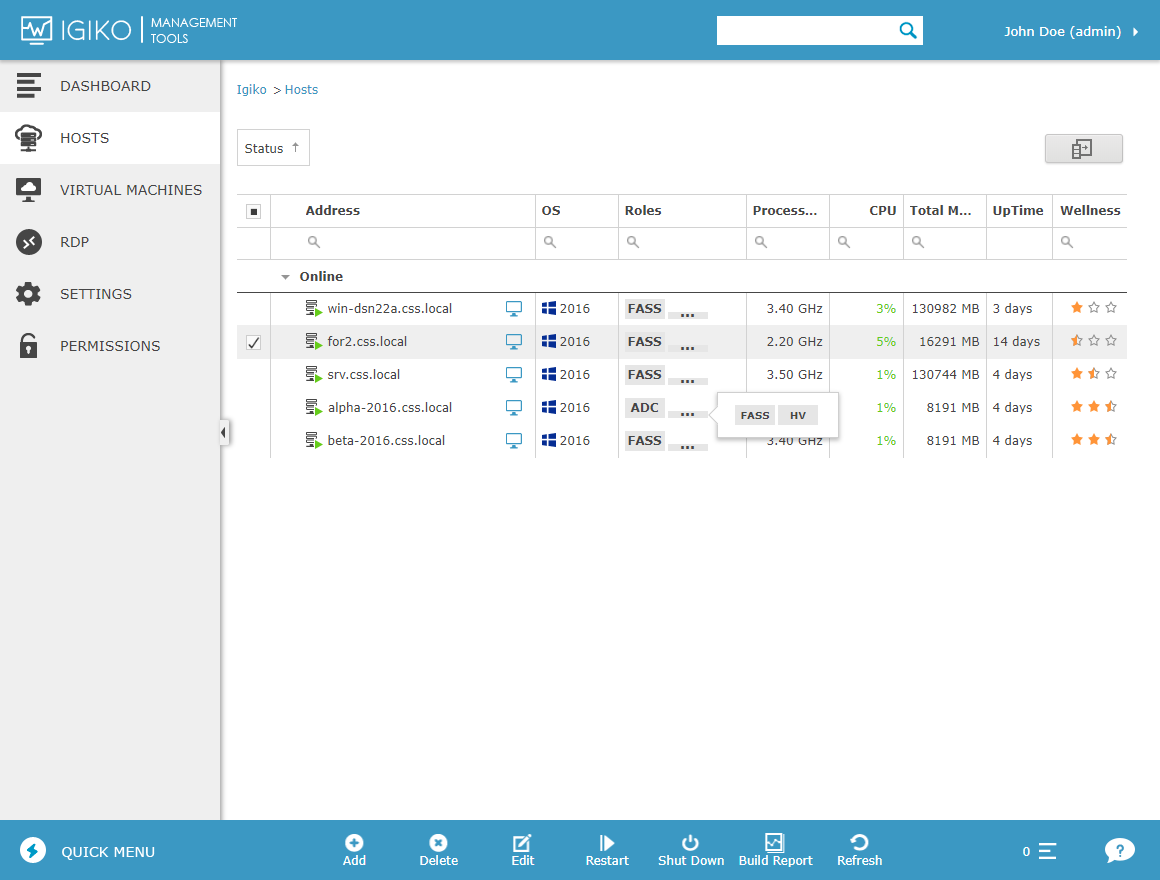
When working with hosts, the following basic operations are available to users: Restart and Shutdown. They can be run immediately or deferred for a user-defined interval. If you choose the latter, you can change the settings of operation start time or cancel it entirely by going to the host page and selecting the Scheduler tab. Please note that, if you have no physical access to the host, you won’t be able to start it remotely after executing the Shutdown command. In future app versions, this will be possible by using specially configured network packets.
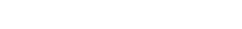
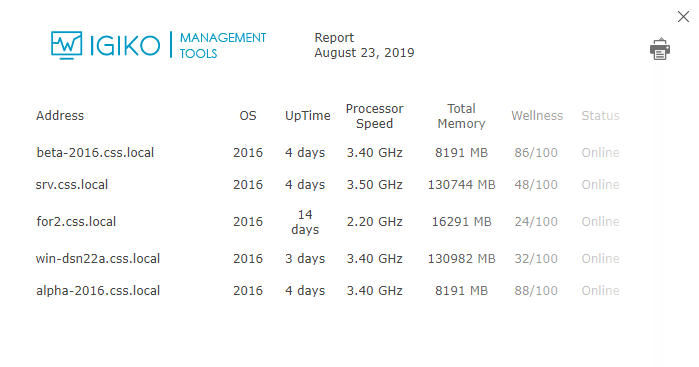
These operations are available both on the page with a list of hosts (where you can put a check mark next to multiple host names at once and run the operation), and on individual host pages. When working with the list of hosts, you can use an additional operation named Build Report: you can select the information to be displayed for hosts and will get data in table form optimized for output to printer.
You can also connect to a host’s desktop with just one click by using the RDP Gateway built into Igiko. This operation is available on the host page in the action bar and on the page with the list of hosts as an icon next to the host name. For information about how to use the RDP Gateway, its settings and specifics of use, see this article.
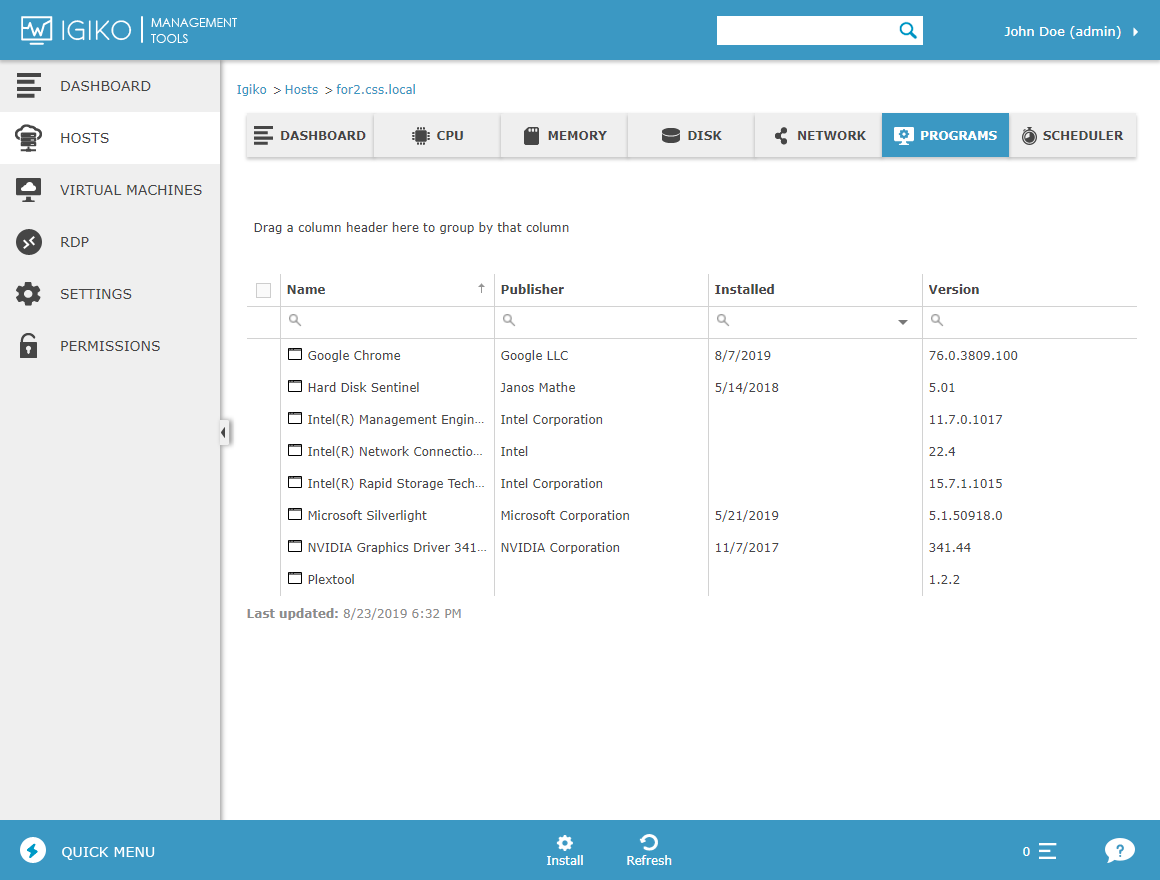
Users can remotely install and delete software to/from hosts. However, there’s a number of restrictions. The app installer must be in MSI format and support silent installation mode. The installer file itself must be saved to a location that can be accessed from the host. This can be the host’s disk or a network folder. You can delete apps which were initially installed via MSI and some other apps that support silent uninstall and are properly registered in the registry, such as EXE installers based on InnoSetup. In the future, we plan to enhance Igiko’s app installation functionality to include all EXE installers.
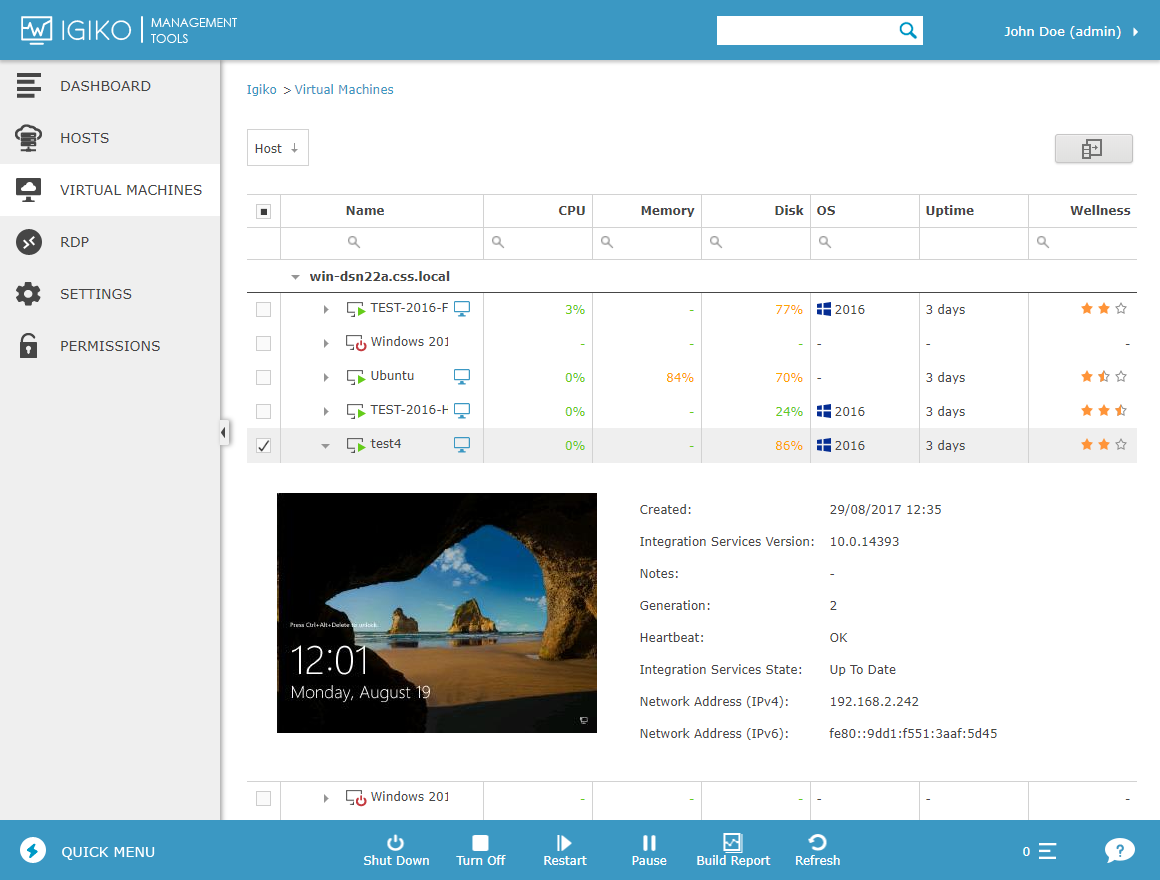
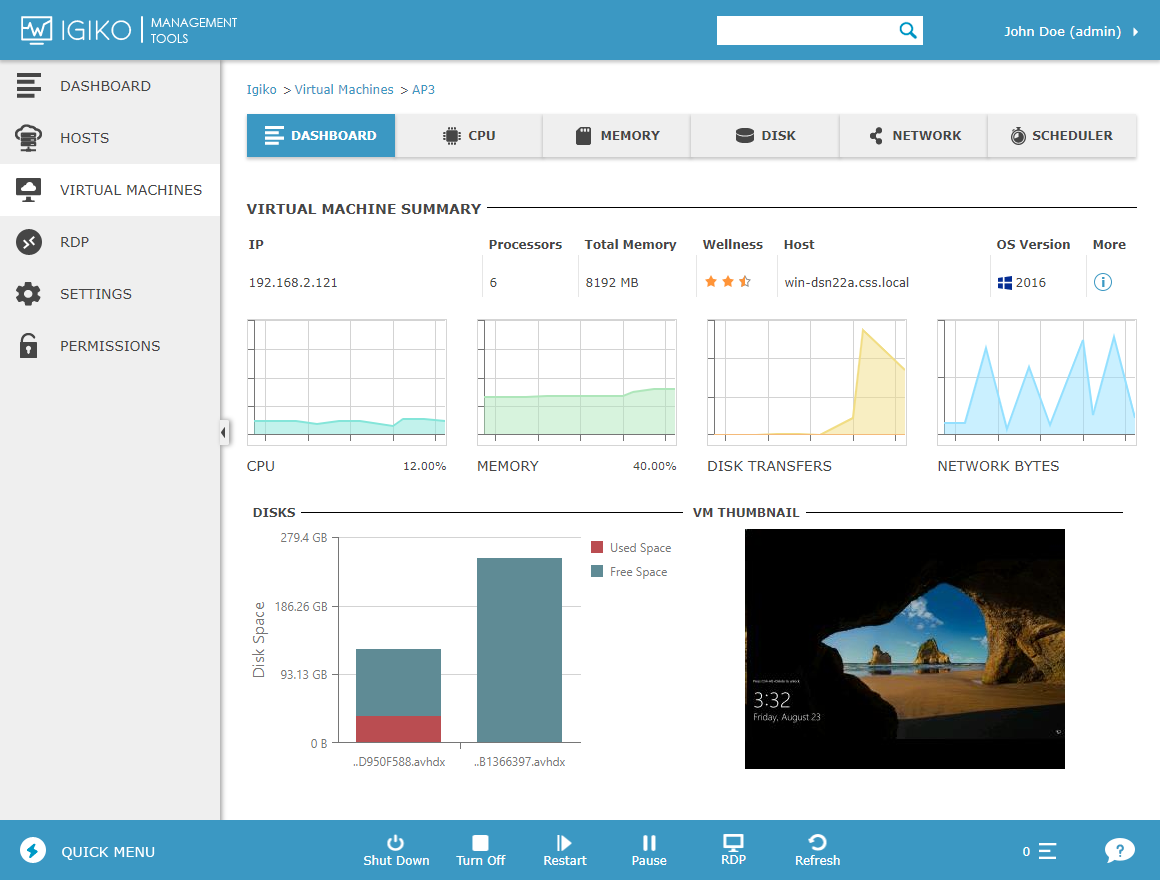
What regards VMs, more operations are supported and, in addition to Shutdown and Restart, you can perform such operations as Turn Off, Start, Pause, and Resume. Similarly to host operations, you can do that from the page with a list of VMs and from the page of a specific VM; operations can be run both immediately and scheduled for a later time.
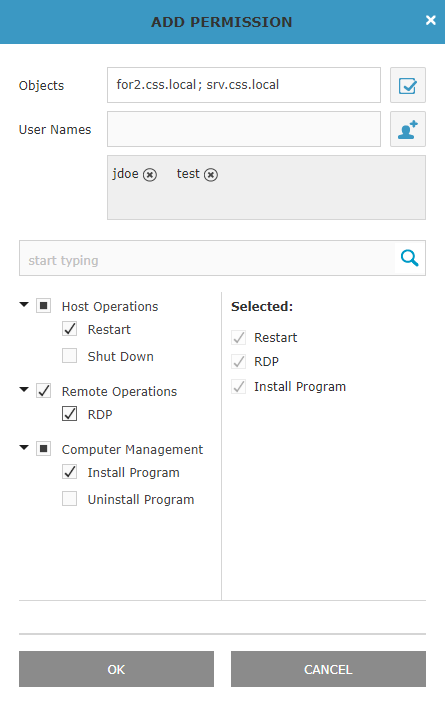
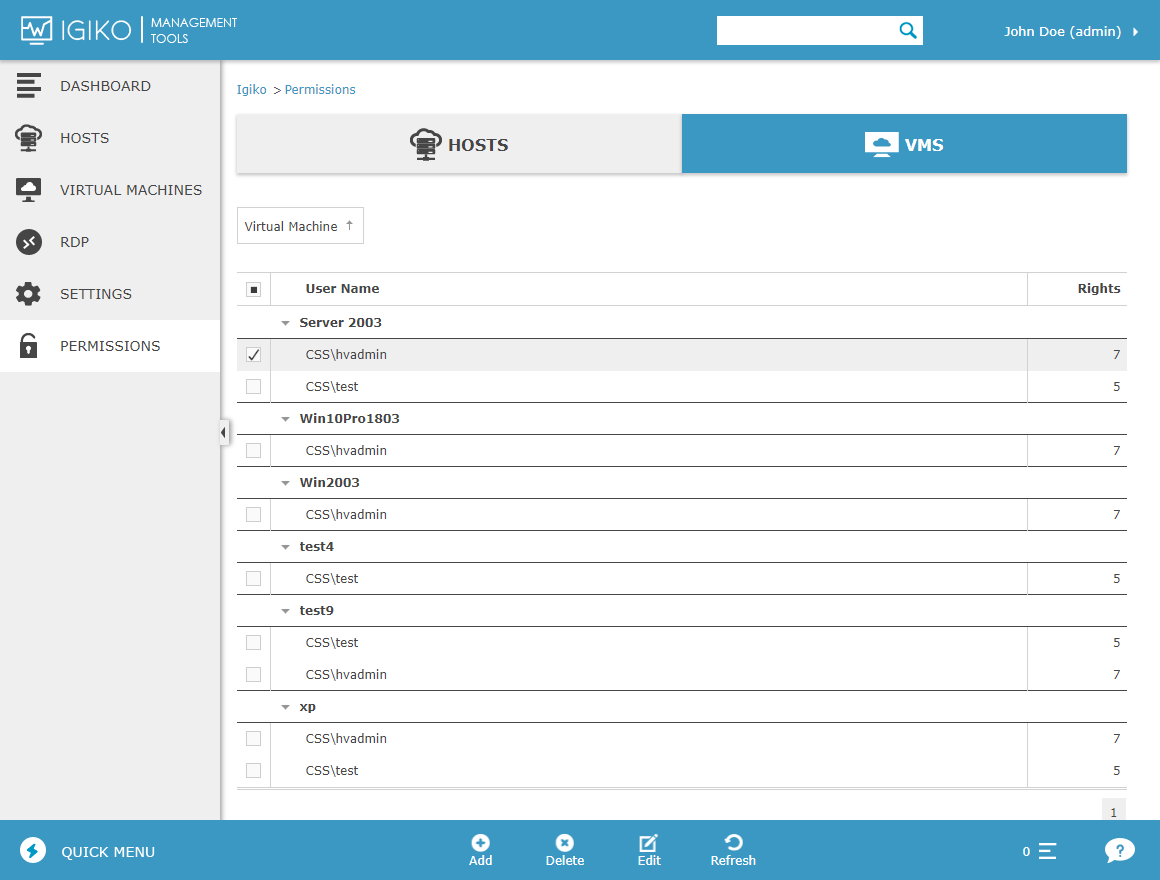
All the above operations are always available to administrators. To enable a user to work with objects and perform operations, explicitly delegate them the appropriate permissions. This is done on the Permissions tab. Click Add and select the necessary objects (hosts or VMs – separately on individual tabs), the users you grant access to these objects, and a set of operations they are allowed to perform. If you don’t add a certain operation to the user, it won’t be available via the interface. It should be noted that Igiko users will have admin rights only if the domain user is in the Active Directory, the Domain Admins group.
Please keep in mind that, in the current version of the app, user authentication is done only using Windows Authentication. In other words, if a user opens a browser with the app when working on their PC in the domain, they will be automatically authenticated under the current user. If it’s a remote session, i.e., the browser user is currently outside the operational domain, the browser will request the user to enter the domain credentials for password-based authentication.